POPULAR
How to Secure Linux & Windows Servers with Fortinet Firewalls
Secure Linux & Windows servers with Fortinet firewall rules.
FortiGate Firewalls Compared: FG-200E, FG-120G, and FG-200F
IntroductionIn the world of cybersecurity, one of the most critical decisions an organization can make is choosing the right firewall. Fortinet's FortiGate series offers a range of options, each with its own strengths…
How P J Networks’ Firewalls Ensure Compliance with the Latest Data Protection Regulations
Keeping up with evolving data protection regulations such as GDPR and CCPA is crucial for businesses. This article discusses how P J Networks’ firewall solutions help organizations stay compliant by enforcing security…
How Quantum-Resistant Firewalls Will Secure Networks Against Future Quantum Threats
How Quantum-Resistant Firewalls Will Secure Networks Against Future Quantum Threats Let's face it—quantum computing isn't just some sci-fi fever dream anymore. It's real, it's coming, and it's about…
Step-by-Step Guide to Configuring Your Firewall for Small Business Security
Follow this step-by-step guide to configure your firewall for maximum protection in small business environments.
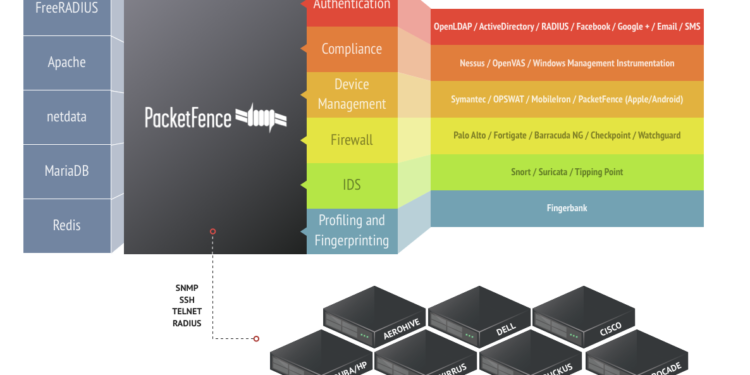
Which Open Source NAC is good
There are many good open source NAC solutions available, but some of the most popular include:PacketFence: PacketFence is a comprehensive NAC solution that offers a wide range of features, including endpoint compliance…
How P J Networks’ Firewalls Secure Virtual Private Networks (VPNs)
Secure remote access is critical in today's work environment. This article discusses how P J Networks’ firewall solutions enhance VPN security, ensuring safe and encrypted connections for remote users, and provides case…
Getting Started with Netskope: A Step-by-Step Guide
Netskope Basics - Step by Step Guides Introduction Cybersecurity is important in the digital space now-a-days. Given the reality that so many companies are being forced into remote work - requiring new and fulfillable…
How to Use SIEM for Firewall Log Analysis
SIEM tools make firewall log analysis more effective.